Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Are Cloud-Based Services Overhyped?
| Read |
|
Articles:
What if it Rains in the Cloud?
| Read |
| Read | |
| Read | |
|
Articles:
Email Security - Can't Live Without It!
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
Network Protocol Analyzers
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
Network Protocol Analyzers
Detect Brute-Force Attacks with nChronos Networ...
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/d...

ManageEngine Firewall Analyzer
Ensuring Compliance and Business Continuity in ...
In the wake of digital transformation, the work landscape as we know it has undergone a dynamic shift. People can now work from home, from the offi...
Network Protocol Analyzers
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
Featured Subcategories:
WireShark Articles:
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Your IP address:
18.226.159.74
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Palo Alto Networks
Palo Alto Firewall Application-based Policy Enforcem...
Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with th...
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mode, ...
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain th...
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...
Windows Servers
Free Webinar: Scripting & Automation in Hyper-V with...
System Center Virtual Machine Manager (SCVMM) provides some great automation benefits for those organizations that can afford the hefty price tag. Howev...
Windows Servers
How to Enable ‘Web Server’ Certificate Template Opti...
In this article we will show you how to enable the ‘Web Server’ certificate template option on a Windows Certification Authority (Windows CA) Server.&nb...
Windows Servers
New Upcoming Features in Hyper-V vNext - Free Train...
With the release of Hyper-V vNext just around the corner, Altaro has organized a Free webinar that will take you right into the new Hyper-V vNext releas...
Windows Servers
Troubleshooting Windows Server 2012 R2 Crashes. Anal...
There are umpteen reasons why your Windows Server 2012 R2 decides to present you with a Blue Screen of Death (BSOD) or the stop screen. As virtual machi...
Popular Topics
Routing
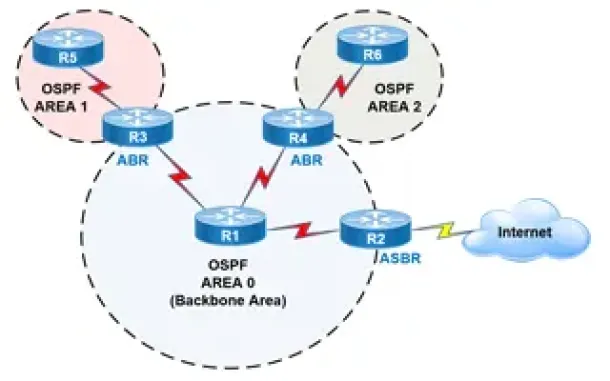
OSPF - Part 2: How OSPF Protocol Works & Basic Conce...
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose ...
Windows Servers
Windows Server 2016 – Hyper-V Virtualization Update
The new Hyper-V virtualization features offered by Windows Server 2016 are planning to make major changes in the virtualization market. From Nested Hype...
Virtualization & VM Backup
SysAdmin Day 2020 - Get your Free Amazon Voucher & G...
SysAdmin Day has arrived, and with it, gratitude for all the unsung heroes that 2020 has needed. Your hard work has made it possible for all of us to ke...
SASE & SD-WAN Networks
SD-WAN is the Emerging, Evolving Solution for the Br...
A lot has changed in how people work during the past twenty years. Co-working spaces, mobility, and the cloud now are common. Businesses are spread out ...
Cisco Switches
Cisco Catalyst Err-disabled Port State, Enable & Dis...
Errdisable is a feature that automatically disables a port on a Cisco Catalyst switch. When a port is error disabled, it is effectively shut down a...
Cisco CallManager-CCME
How To Upgrade Cisco - Linksys SPA8000 Firmware
The Cisco - Linksys SPA8000 is an 8-port IP Telephony Gateway that allows connections for up to eight analog telephones (provides 8 FXS ports) to a VoIP...
Cisco Firewalls
Understand & Configure NAT Reflection, NAT Loopback,...
This article examines the concept of NAT Reflection, also known as NAT Loopback or Hairpinning, and shows how to configure a Cisco ASA Firewall running ...
Cisco Routers
How To Secure Your Cisco Router Using Cisco AutoSecu...
In today’s complex network environments securing your network routers can be a daunting task, especially when there are so many CLI commands and paramet...




















