Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Firewall.cx Free Cisco Lab: Our Partners
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...

ManageEngine Firewall Analyzer
Dealing with Security Audit Challenges: Discove...
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifyi...
Network Protocol Analyzers
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
OpManager - Network Monitoring & Management
Ensuring Enterprise Network Readiness for Mobil...
Demands for Enterprise networks to properly support mobile users is on a continuous rise making it more than ever necessary for IT departments to p...
Featured Subcategories:
WireShark Articles:
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
Improve Network Analysis Efficiency with Colaso...
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network...
Detect Brute-Force Attacks with nChronos Networ...
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/d...
Your IP address:
3.145.2.184
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Complete Guide to Upgrading Palo Alto Firewall PAN-O...
Upgrading your Palo Alto Firewall or Panorama Management System to the preferred PAN-OS release is always recommended as it ensures it remains stable, s...
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtu...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fi...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup with A...
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization platf...
Windows Servers
New Features in Windows Server 2012 - Why Upgrade t...
There is no doubt that Cloud Computing is hot topic these days. Innovations in cloud computing models have made every industry and company IT department...
Windows Servers
Free Webinar: Troubleshooting & Fixing Microsoft Hyp...
Users working with Hyper-V Virtualization would be interested to know that Altaro is hosting a free webinar on the 25th of February 2016 at 4pm CET / 10...
Windows Servers
Free Webinar: Scripting & Automation in Hyper-V with...
System Center Virtual Machine Manager (SCVMM) provides some great automation benefits for those organizations that can afford the hefty price tag. Howev...
Popular Topics
Windows Servers
How to Easily Change Network Card Profile / Network ...
Network Location Awareness (NLA) is a feature offered on Windows Server 2012 R2 and all Windows workstation editions from Windows 8.1 and above, includi...
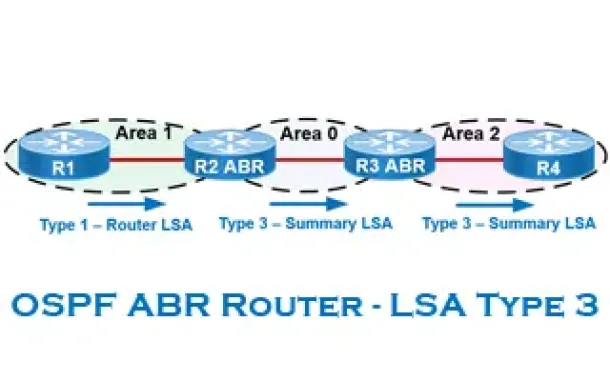
Routing
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Virtualization & VM Backup
The Backup Bible. A Free Complete Guide to Disaster ...
The Free Backup Bible Complete Edition written by backup expert and Microsoft MVP Eric Siron, is comprised of 200+ pages of actionable content divided i...
Windows Servers
Free Hyper-V eBook - Create, Manage and Troubleshoot...
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to co...
Cisco CallManager-CCME
How to Enable & Disable Phone Port Lines on Cisco AT...
The Cisco ATA 186 and 188 analog phone adaptor is very common amongst Cisco CallManager (CUCM) & Cisco CallManager Express (CUCME) installations.
T...
Cisco Wireless
Easily Convert Cisco Autonomous - Standalone AP to L...
This article explains how to convert a local or remote Autonomous / Standalone Cisco Aironet Access Point to Lightweight and register it to a Cisco WLC ...
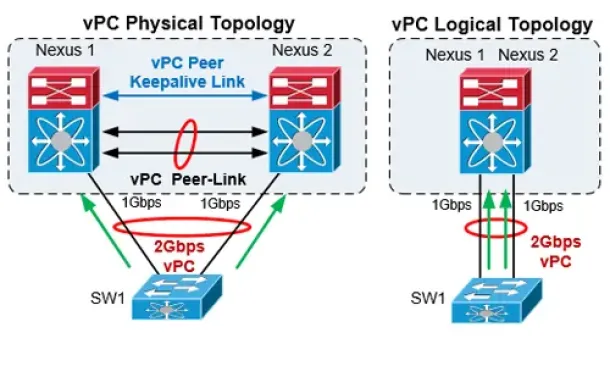
Cisco Data Center (Nexus/UCS)
The Complete Cisco Nexus vPC Guide. Features & Advan...
Cisco virtual Port Channel (vPC) is a virtualization technology, launched in 2009, which allows links that are physically connected to two different Cis...
Cisco Switches
Configuring SPAN On Cisco Catalyst Switches - Monito...
Being able to monitor your network traffic is essential when it comes to troubleshooting problems, performing a security audit or even casually checking...




















