Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Introduction to Routing Protocols
| Read |
| Read | |
|
Articles:
Interior Gateway Protocol - IGRP
| Read |
| Read | |
|
Articles:
Routing Information Protocol - RIP
| Read |
| Read | |
|
Articles:
Link State Routing Protocols
| Read |
|
Articles:
Distance Vector Routing Protocols
| Read |
| Read | |
|
Articles:
Routed Protocols
| Read |
Suggested Articles:
Network Cabling
CAT5, CAT5e, CAT6 UTP X-Over / Cross-over Cable
The cross-over (or crossover) CAT5 UTP cable has to be one of the most used cables after the classic straight-thru cable. The cross-over cable allo...
The OSI Model
The OSI Model: Layer 4 - Transport Layer
The Transport layer is responsible for providing mechanisms for multiplexing upper-layer application, session establishment, data transfer and tear...
Network Protocols
Understanding VPN IPSec Tunnel Mode and IPSec T...
IPSec’s protocol objective is to provide security services for IP packets such as encrypting sensitive data, authentication, protection against rep...
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 3: The TCP...
This article shows the TCP Header and Segment. We explain where the TCP Header and Segment are located in an Ethernet frame and also briefly view t...
Featured Subcategories:
Netflow Articles:
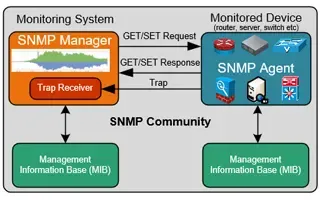
Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...
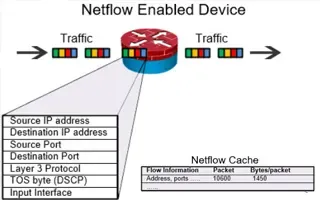
Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Your IP address:
3.145.38.117
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative over...

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Sta...
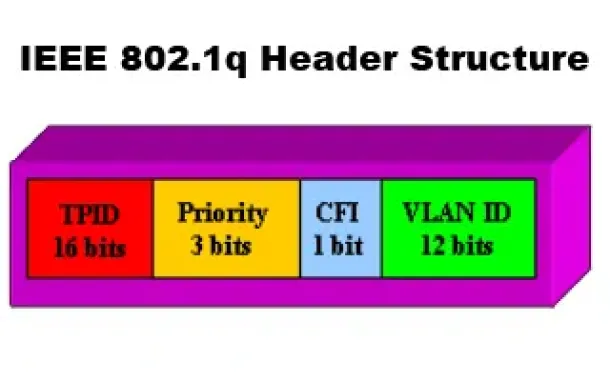
VLAN Networks
VLANs - IEEE 802.1q Trunk Link Protocol Analysis
While the VLAN Tagging article briefly covered the IEEE 802.1q protocol this article will continue building upon it by further analyzing the IEEE 802.1q...

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trun...
Routing
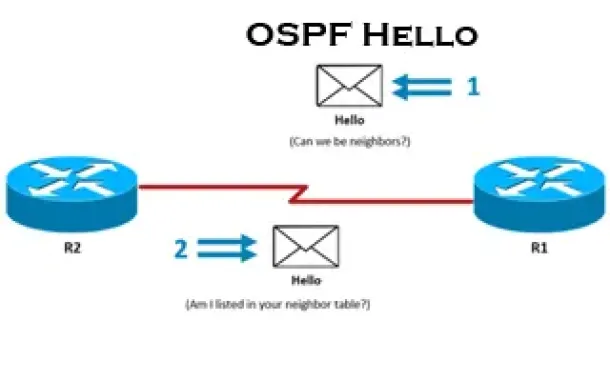
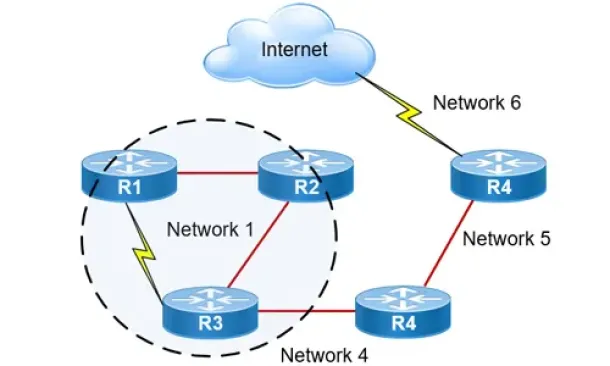
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Pro...
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll exami...
Routing
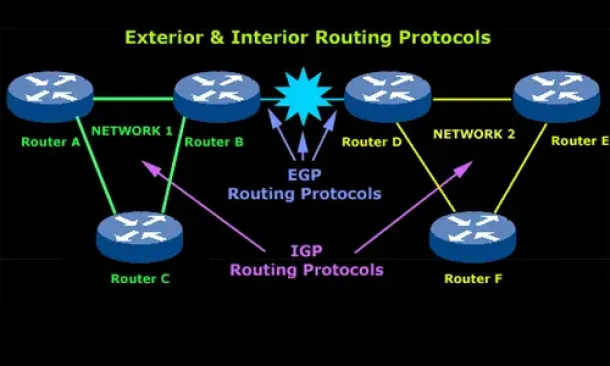
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchan...
Routing
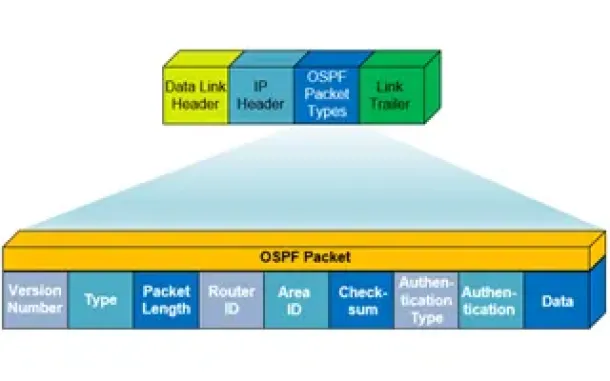
OSPF - Part 1: Introduction, OSPF Packet Structure, ...
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) worki...
Routing
Hybrid Routing Protocols - Advantages and Disadvanta...
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scala...
Cisco Switches
VLAN Security Tips - Best Practices
This article focuses on VLAN Security and its implementation within the business network environment. We provide tips and Cisco CLI commands that will h...
Cisco Wireless
Wireless (Wifi) WEP WPA WPA2 Key Generator
The Firewall.cx Wireless LAN Key Generator will allow the generation of a WEP or WPA ASCII based encryption key and will provide the equivalent HEX o...
Windows Servers
Windows Server 2016 – Hyper-V Virtualization Update
The new Hyper-V virtualization features offered by Windows Server 2016 are planning to make major changes in the virtualization market. From Nested Hype...
Cisco Routers
Configuring Cisco SSL VPN AnyConnect (WebVPN) on Cis...
Our Web SSL VPN article written back in 2011 introduced this new wave of VPN services. This article extends the topic by covering the installation...




















